ISO 27001
Same graph, same evidence model, same approval contract. Adding a framework is a mapping exercise, not a new product.
OrbisGraph turns your IT security concept into a structured knowledge graph. Every claim is traceable to source. Every key decision needs human sign-off. Every AI inference is measured against a benchmark.
02 / The thesis
For thirty years, IT-Grundschutz has lived in Word and Excel. OrbisGraph moves it into a structure a machine can read.
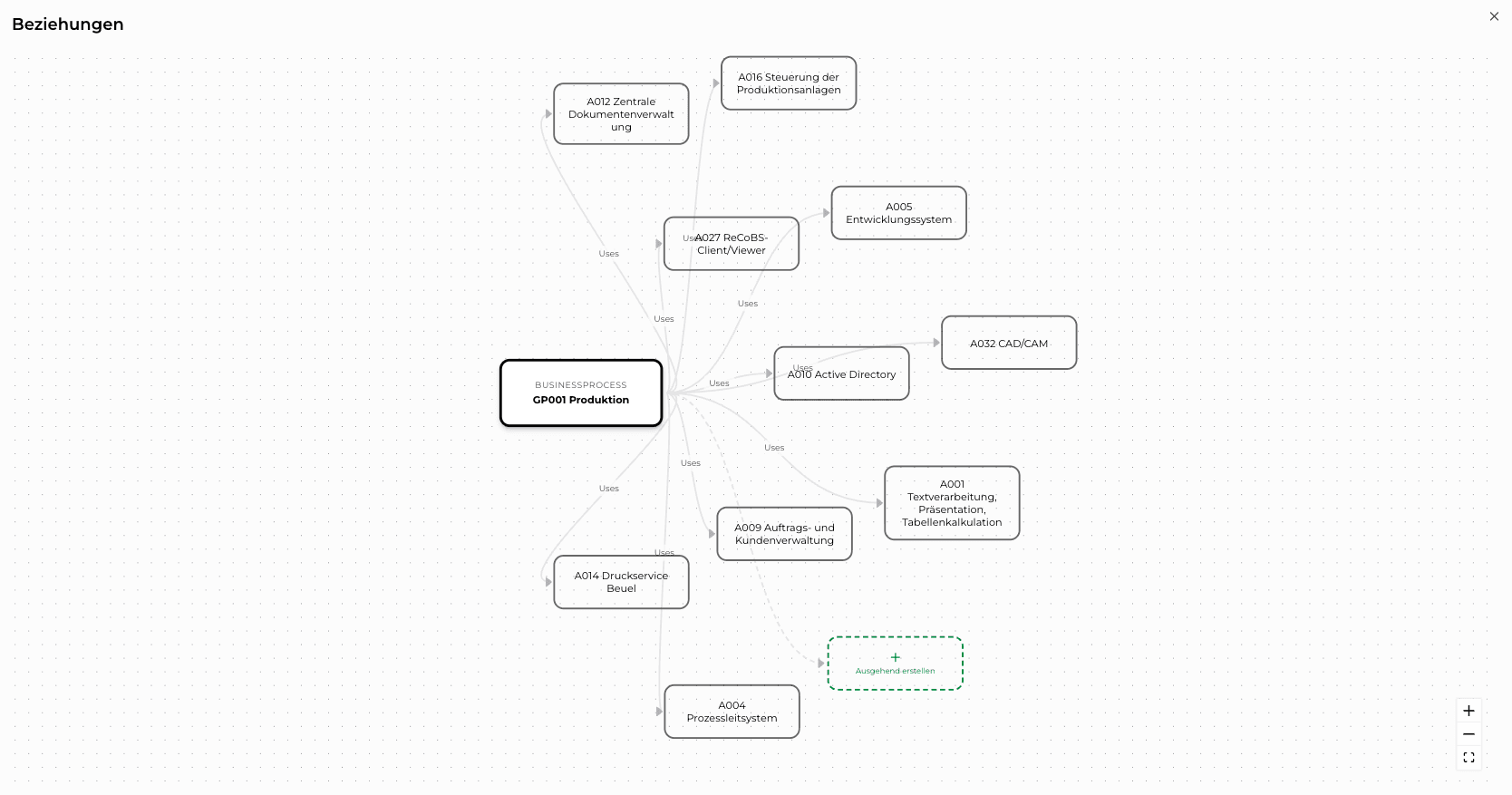
Processes, applications, systems, networks, rooms, and buildings become nodes on a graph. BSI Bausteine attach to the nodes they apply to. Evidence attaches to the Bausteine.
Specialised AI models build the graph and query it. Your team signs off on key decisions. The auditor reads the trail back.
03 / In production
In production today. Full BSI methodology: Strukturanalyse, Schutzbedarfsfeststellung, Modellierung, Grundschutz-Check, Risikoanalyse.
See the workflowPreparedThe platform is graph-native, so the step to the BSI's machine-readable format is a serialisation exercise, not a rewrite.
See the readiness briefSame graph, same evidence model, same approval contract. Adding a framework is a mapping exercise, not a new product.
Where most customers start. Sovereign German infrastructure, German data residency, no transatlantic path for the graph or for inference.
SaaS orchestration on Deutsche Telekom Cloud. Inference endpoints inside your perimeter. Your documents never leave your network; only graph operations cross the boundary.
Graph, weights, and inference on your infrastructure. Terraform-based redeployment, air-gap capable, BYOK. Designed for KRITIS, telecom under §109 TKG, and public-sector clients.
Operated under a large consultancy's brand. Separate namespace, same graph engine, same approval contract.
04 / The workflow
OrbisGraph follows BSI 200-2 and 200-3. Each phase is handled by specialised AI agents, then approved by your team before it lands in the graph. The numbers below are measured against the manual baseline on the same project.
A1 · BSI 200-2
Ingests your documentation: organisational descriptions, network diagrams, asset inventories. Builds the graph. Every extracted entity links back to the sentence that produced it.
Measured on the same project
05 / Quality assurance
The failure mode of AI in compliance is not that it can't write a control text. It's that it writes one that reads plausible but is wrong. We built the system against exactly that.
Every Umsetzungstext links to its source passage with a SHA-256 hash. If the source changes, the hash breaks and the linked text gets flagged for review. Provenance is the default state.
Every AI output carries a confidence score. Low-confidence outputs are flagged, not silently accepted. Approval is required at every phase boundary. Nothing advances on inference alone.
Extraction quality is independently validated by cybersecurity researchers at Freie Universität Berlin, measured on real Grundschutz corpora.
Benchmarked on real Grundschutz corpora by cybersecurity researchers at Freie Universität Berlin
Where the model is uncertain, it flags; it does not guess. Both numbers improve with every model iteration.
06 / AI architecture
An IT security concept pulls from two kinds of knowledge. The BSI side: Bausteine, requirements, the 200-2 / 200-3 methodology. Your side: processes, applications, systems, policies, people.
OrbisGraph keeps each side in its own AI expert. The orchestrator routes work to the BSI phase that owns it; inside each phase, a specialised ensemble classifies, parses, extracts, and validates. Every agent sees only what it needs, and nothing commits without human approval.
The architecture is HybridRAG: retrieval-augmented generation runs against a structured knowledge graph for deterministic data representation.
Takes a request, breaks it into sub-tasks, routes each one to the right experts and agents. Tracks approval across phases. Handles concurrent writes.
It does not draft, score, or decide. It coordinates.
The IT-Grundschutz Expert holds the BSI Compendium, Bausteine, requirements, and the 200-2 / 200-3 methodology. The Enterprise Expert models your organisation: documents, entities, approved policies. Every agent in every phase consults both before writing.
A1 to A5: Strukturanalyse, Schutzbedarfsfeststellung, Modellierung, Grundschutz-Check, Risikoanalyse. Each phase runs its own ensemble of specialised agents — classifiers, extractors, validators — sized to the phase. Strukturanalyse and Grundschutz-Check, the most demanding, run the deepest ensembles.
Nothing lands in the graph without Approval.
See the architecture run on your own Sicherheitskonzept.
Book a demo07 / Grundschutz++-readiness
Grundschutz++ replaces document-centric compliance with machine-readable, structured data. OrbisGraph is architecturally native to this direction. Concepts built today convert when the new format ships, no restart required. The same graph-native structure makes ISO 27001 a serialisation exercise, not a rebuild.
Read the briefing08 / Credibility
Sovereign German hosting. Your data stays in Germany, on Deutsche Telekom Cloud.
Platform detailsExtraction quality is independently validated by cybersecurity researchers at Freie Universität Berlin.
Platform detailsFounded by cryptography, AI, and cybersecurity researchers. German GmbH, headquartered in Berlin.
Meet the team09 / Funded by
A funding line for innovation with national economic relevance.
The OrbisGraph IT-Grundschutz module is built with support from the Innovation Programme for Business Models and Pioneering Solutions (IGP) of the German Federal Ministry for Economic Affairs and Energy, a funding line for innovation with national economic relevance.
Project reference available on request · Contact →
Schedule a call to explore how OrbisGraph can accelerate your compliance efforts.